What is IVRE?
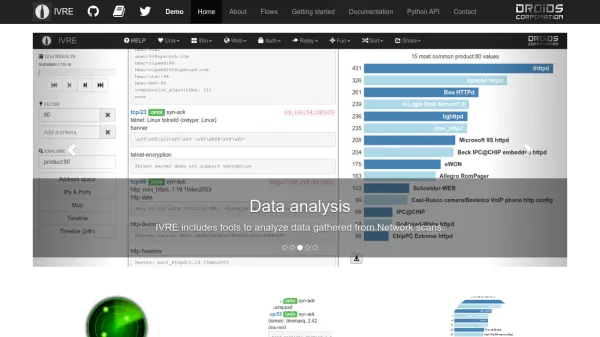
IVRE is an open-source framework for network reconnaissance, written in Python with a MongoDB backend. It provides tools to gather network intelligence using well-known tools like Nmap, Masscan, ZGrab2, ZDNS, and Zeek (Bro). The platform stores scan results in a database and offers multiple interfaces—CLI, Python API, and a Web interface—for browsing, filtering, and analyzing the data.
IVRE includes a dedicated Web interface for analyzing Nmap scan results, which can handle massive scans more efficiently than traditional GUI tools. It also supports flow analysis by importing data from Zeek (Bro), Argus, or Nfdump, allowing users to explore network flows from a CLI, Web interface, or Python API. The framework is freely available on GitHub and can be installed via distribution packages, Pip, Docker, or manual setup.
Features
- Scan & Sniff: Run Nmap scans against targets like networks, countries, AS, or full IPv4 space; parse output from Masscan, ZGrab2, ZDNS; collect passive traffic info using Zeek (Bro), Argus, Nfdump.
- Browse: Use CLI tools, Python API, or Web interface to browse results, filter for specific services or vulnerable versions, search by country or network, and access previous results for specific hosts.
- Analyze: Identify similar hosts and corner-cases, find most and least common ports, services, or products, and get a quick overview with the heatmap feature.
- Flow Analysis: Import network flows from Zeek (Bro), Argus, or Netflow (Nfdump); explore data from CLI, Web interface, and Python API.
Use Cases
- Network reconnaissance and mapping
- Vulnerability assessment and management
- Security monitoring and flow analysis
- Large-scale internet scanning research
- Threat intelligence integration with YETI and Cortex
FAQs
-
What databases does IVRE support?
IVRE uses MongoDB as the recommended backend for storing scan results and flow data. -
Can IVRE handle full IPv4 scans?
Yes, IVRE can run Nmap scans against the full IPv4 connected address space and parse results from Masscan. -
How do I install IVRE on Kali Linux?
On Kali Linux, run 'apt install ivre' to install the package. You can also add 'ivre-doc' if needed. -
Does IVRE integrate with other security tools?
Yes, IVRE integrates with YETI (Your Everyday Threat Intelligence) and Cortex (TheHive project). -
What is the meaning of the name IVRE?
IVRE stands for 'Instrument de veille sur les réseaux extérieurs' in French, and is also a play on 'DRUNK' (Dynamic Recon of Unknown NetworKs).