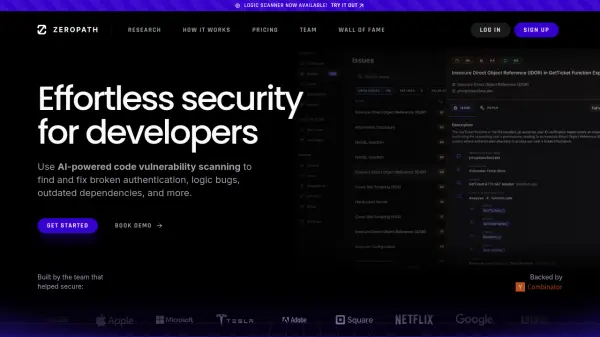
What is ZeroPath?
ZeroPath provides an AI-driven platform designed to enhance application security for development teams. It integrates directly into existing CI/CD pipelines, supporting environments like Github, GitLab, and BitBucket. The system focuses on identifying complex security vulnerabilities, including broken authentication mechanisms, business logic flaws, and insecure dependencies, aiming for higher accuracy and fewer false positives compared to traditional scanning tools.
The platform is built for speed, with security checks typically completing in seconds to avoid slowing down the development process. Instead of merely reporting issues and adding to backlogs, ZeroPath distinguishes itself by automatically generating pull requests (PRs) with proposed patches for identified vulnerabilities when confident these changes won't disrupt the application's functionality. This approach streamlines the remediation process, embedding security seamlessly into development practices.
Features
- AI-Powered SAST: Performs static application security testing enhanced by AI, finding more bugs with fewer false positives.
- Broken Authentication Detection: Finds and helps fix broken or missing authorization (authZ) and authentication (authN).
- Business Logic Flaw Detection: Identifies critical flaws in application logic often missed by other scanners.
- Software Composition Analysis (SCA): Scans dependencies for vulnerabilities, incorporating reachability and exploitability analysis.
- Secrets Detection: Locates exposed secrets with validation processes to minimize false positives.
- IaC Security Scanning: Checks Infrastructure as Code configurations (e.g., Terraform, CloudFormation) for security vulnerabilities.
- Automated Patch Generation: Automatically generates pull requests with suggested code fixes for certain vulnerabilities.
- CI/CD Integration: Seamlessly integrates into existing CI/CD pipelines (GitHub, GitLab, Bitbucket).
- Intelligent Severity Assessment: Accurately assesses and prioritizes security risks.
- PR Code Reviews: Provides automated security reviews within pull requests.
Use Cases
- Automating security scanning within CI/CD pipelines.
- Identifying and fixing complex vulnerabilities like logic flaws and broken authentication.
- Reducing security debt by automatically generating patches for vulnerabilities.
- Securing software supply chains through advanced dependency scanning.
- Improving development speed by integrating fast, low-noise security checks.
- Enhancing Infrastructure as Code (IaC) security posture.
- Providing continuous application security monitoring.
Related Queries
Helpful for people in the following professions
ZeroPath Uptime Monitor
Average Uptime
0%
Average Response Time
0 ms