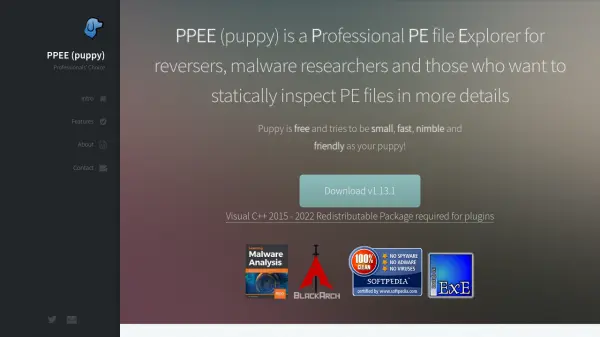
What is PPEE (puppy)?
PPEE (puppy) is a Professional PE file Explorer tool specifically designed for security professionals who need to analyze Windows Portable Executable (PE) files. This lightweight application provides comprehensive static analysis capabilities for examining executable files in detail, making it particularly valuable for malware research and reverse engineering tasks.
The tool supports analysis of both PE32 and PE64 file formats and includes features for examining all PE directories including Export, Import, Resource, Exception, Certificate, Base Relocation, Debug, TLS, Load Config, Bound Import, IAT, Delay Import, and CLR (.Net) directories. It offers robust parsing capabilities for various file types including exe, dll, sys, scr, drv, cpl, and ocx files, with built-in tools for hash calculation, string analysis, and anomaly detection.
Features
- PE File Analysis: Supports both PE32 and PE64 file formats with robust parsing of exe, dll, sys, scr, drv, cpl, and ocx files
- Security Integration: Includes Virustotal and OPSWAT's Metadefender query capabilities for malware detection
- Comprehensive Inspection: Examines all PE directories including Export, Import, Resource, Exception, Certificate, Base Relocation, Debug, TLS, Load Config, Bound Import, IAT, Delay Import and CLR (.Net)
- Hash Calculation: Provides entropy, SSDEEP, TLSH, CRC32, ImpHash, MD5, SHA1, SHA256 and Authentihash calculation for files and sections
- String Analysis: Views embedded strings including URL, Registry, Suspicious patterns, and other artifacts within files
Use Cases
- Malware analysis and detection for security researchers
- Reverse engineering of Windows executable files
- Static analysis of suspicious binaries for threat detection
- Examination of PE file structures for software development
- Security auditing of executable files for compliance purposes
Helpful for people in the following professions
PPEE (puppy) Uptime Monitor
Average Uptime
0%
Average Response Time
0 ms