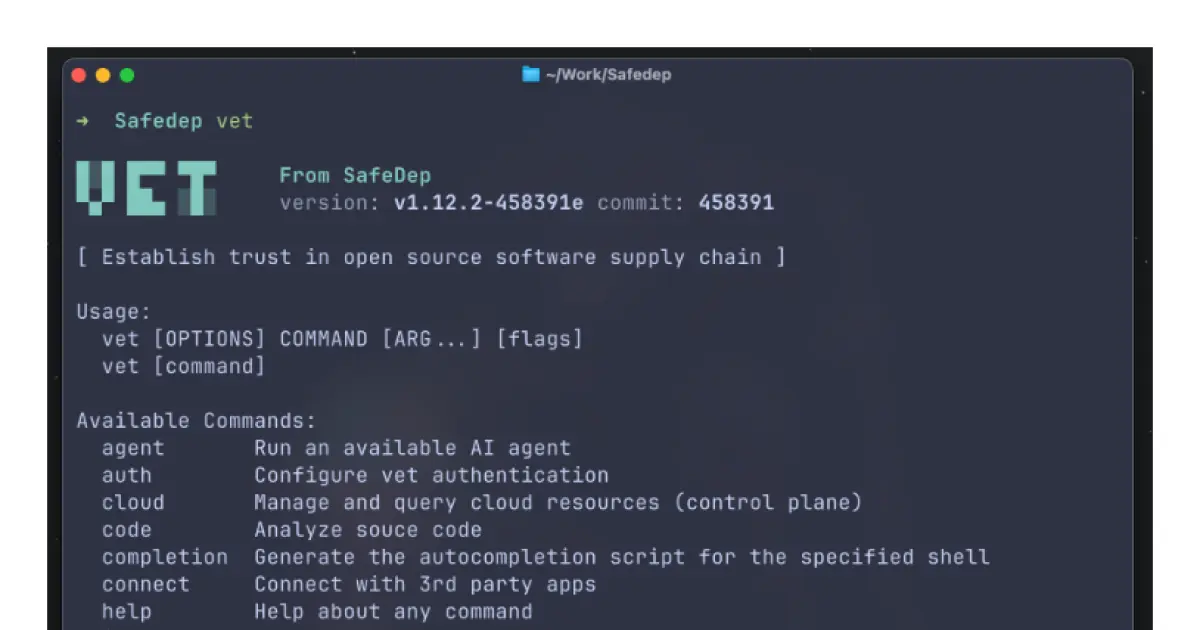
SafeDep VET
Enterprise-grade open source software supply chain security with MCP capabilities.
Key Features
Use Cases
README
🎯 Why vet?
70-90% of modern software constitute code from open sources — How do we know if it's safe?
vet is an open source software supply chain security tool built for developers and security engineers who need:
✅ Next-gen Software Composition Analysis — Vulnerability and malicious package detection
✅ Policy as Code — Express opinionated security policies using CEL
✅ Real-time malicious package detection — Powered by SafeDep Cloud active scanning
✅ Multi-ecosystem support — npm, PyPI, Maven, Go, Docker, GitHub Actions, and more
✅ CI/CD native — Built for DevSecOps workflows with support for GitHub Actions, GitLab CI, and more
✅ MCP Server — Run vet as a MCP server to vet open source packages from AI suggested code
✅ Agents — Run AI agents to query and analyze scan results
⚡ Quick Start
Install in seconds:
# macOS & Linux
brew install safedep/tap/vet
or download a pre-built binary
Scan your project:
# Scan current directory
vet scan -D .
# Scan a single file
vet scan -M package-lock.json
# Fail CI on critical vulnerabilities
vet scan -D . --filter 'vulns.critical.exists(p, true)' --filter-fail
# Fail CI on OpenSSF Scorecard requirements
vet scan -D . --filter 'scorecard.scores.Maintained < 5' --filter-fail
# Fail CI if a package is published from a GitHub repository with less than 5 stars
vet scan -D . --filter 'projects.exists(p, p.type == "GITHUB" && p.stars < 5)' --filter-fail
🔒 Key Features
🕵️ Code Analysis
Unlike dependency scanners that flood you with noise, vet analyzes your actual code usage to prioritize real risks. See dependency usage evidence for more details.
🛡️ Malicious Package Detection
Integrated with SafeDep Cloud for real-time protection against malicious packages in the wild. Free for open source projects. Fallback to Query Mode when API key is not provided. Read more about malicious package scanning.
📋 Policy as Code
Define security policies using CEL expressions to enforce context specific security requirements.
# Block packages with critical CVEs
vet scan \
--filter 'vulns.critical.exists(p, true)'
# Enforce license compliance
vet scan \
--filter 'licenses.contains_license("GPL-3.0")'
# Enforce OpenSSF Scorecard requirements
# Require minimum OpenSSF Scorecard scores
vet scan \
--filter 'scorecard.scores.Maintained < 5'
🎯 Multi-Format Support
- Package Managers: npm, PyPI, Maven, Go, Ruby, Rust, PHP
- Container Images: Docker, OCI
- SBOMs: CycloneDX, SPDX
- Binary Artifacts: JAR files, Python wheels
- Source Code: Direct repository scanning
🔥 See vet in Action
🚀 Production Ready Integrations
📦 GitHub Actions
Zero config security guardrails against vulnerabilities and malicious packages in your CI/CD pipeline with your own opinionated policies:
- uses: safedep/vet-action@v1
with:
policy: ".github/vet/policy.yml"
See more in vet-action documentation.
🔧 GitLab CI
Enterprise grade scanning with vet CI Component:
include:
- component: gitlab.com/safedep/ci-components/vet/scan@main
🐳 Container Integration
Run vet anywhere, even your internal developer platform or custom CI/CD environment using our container image.
docker run --rm -v $(pwd):/app ghcr.io/safedep/vet:latest scan -D /app
📚 Table of Contents
- 🎯 Why vet?
- ⚡ Quick Start
- 🔒 Key Features
- 🔥 See vet in Action
- 🚀 Production Ready Integrations
- 📚 Table of Contents
- 📦 Installation Options
- 🎮 Advanced Usage
- 📊 Reporting
- 🛡️ Malicious Package Detection
- 📊 Privacy and Telemetry
- 🎊 Community & Support
📦 Installation Options
🍺 Homebrew (Recommended)
brew tap safedep/tap
brew install safedep/tap/vet
📥 Direct Download
See releases for the latest version.
🐹 Go Install
go install github.com/safedep/vet@latest
🐳 Container Image
# Quick test
docker run --rm ghcr.io/safedep/vet:latest version
# Scan local directory
docker run --rm -v $(pwd):/workspace ghcr.io/safedep/vet:latest scan -D /workspace
⚙️ Verify Installation
vet version
# Should display version and build information
🎮 Advanced Usage
🔍 Scanning Options
📁 Directory Scanning
# Scan current directory
vet scan
# Scan a given directory
vet scan -D /path/to/project
# Resolve and scan transitive dependencies
vet scan -D . --transitive
📄 Manifest Files
# Package managers
vet scan -M package-lock.json
vet scan -M requirements.txt
vet scan -M pom.xml
vet scan -M go.mod
vet scan -M Gemfile.lock
🐙 GitHub Integration
# Setup GitHub access
vet connect github
# Scan repositories
vet scan --github https://github.com/user/repo
# Organization scanning
vet scan --github-org https://github.com/org
📦 Artifact Scanning
# Container images
vet scan --image nginx:latest
vet scan --image /path/to/image-saved-file.tar
# Binary artifacts
vet scan -M app.jar
vet scan -M package.whl
🎯 Policy Enforcement Examples
# Security-first scanning
vet scan -D . \
--filter 'vulns.critical.exists(p, true) || vulns.high.exists(p, true)' \
--filter-fail
# License compliance
vet scan -D . \
--filter 'licenses.contains_license("GPL-3.0")' \
--filter-fail
# OpenSSF Scorecard requirements
vet scan -D . \
--filter 'scorecard.scores.Maintained < 5' \
--filter-fail
# Popularity-based filtering
vet scan -D . \
--filter 'projects.exists(p, p.type == "GITHUB" && p.stars < 50)' \
--filter-fail
🔧 SBOM Support
# Scan a CycloneDX SBOM
vet scan -M sbom.json --type bom-cyclonedx
# Scan a SPDX SBOM
vet scan -M sbom.spdx.json --type bom-spdx
# Generate SBOM output
vet scan -D . --report-cdx=output.sbom.json
# Package URL scanning
vet scan --purl pkg:npm/lodash@4.17.21
📊 Query Mode & Data Persistence
For large codebases and repeated analysis:
# Scan once, query multiple times
vet scan -D . --json-dump-dir ./scan-data
# Query with different filters
vet query --from ./scan-data \
--filter 'vulns.critical.exists(p, true)'
# Generate focused reports
vet query --from ./scan-data \
--filter 'licenses.contains_license("GPL")' \
--report-json license-violations.json
📊 Reporting
vet generate reports that are tailored for different stakeholders:
📋 Report Formats
# SARIF for GitHub Security tab
vet scan -D . --report-sarif=report.sarif
# JSON for custom tooling
vet scan -D . --report-json=report.json
# CSV for spreadsheet analysis
vet scan -D . --report-csv=report.csv
# HTML for web-based analysis
vet scan -D . --report-html=report.html
# Markdown reports for PRs
vet scan -D . --report-markdown=report.md
# Console summary (default)
vet scan -D . --report-summary
# SBOM generation
vet scan -D . --report-cdx=sbom.json
# Dependency graphs
vet scan -D . --report-graph=dependencies.dot
🎯 Report Examples
# Multi-format output
vet scan -D . \
--report-json=report.json \
--report-sarif=report.sarif \
--report-markdown=report.md \
--report-html=report.html
# Focus on specific issues
vet scan -D . \
--filter 'vulns.high.exists(p, true)' \
--report-json=report.json
🤖 MCP Server
vet can be used as an MCP server to vet open source packages from AI suggested code.
# Start the MCP server with SSE transport
vet server mcp --server-type sse
For more details, see vet MCP Server documentation.
🤖 Agents
See vet Agents documentation for more details.
🛡️ Malicious Package Detection
Malicious package detection through active scanning and code analysis powered by
SafeDep Cloud. vet requires an API
key for active scanning of unknown packages. When API key is not provided, vet will
fallback to Query Mode which detects known malicious packages from SafeDep
and OSV databases.
- Grab a free API key by running
vet cloud quickstart - API access is free forever for open source projects
- No proprietary code is collected for malicious package detection
- Only open source package scanning from public repositories is supported
🚀 Quick Setup
Malicious package detection requires an API key for SafeDep Cloud.
# One-time setup
vet cloud quickstart
# Enable malware scanning
vet scan -D . --malware
# Query for known malicious packages without API key
vet scan -D . --malware-query
Example malicious packages detected and reported by SafeDep Cloud malicious package detection:
- MAL-2025-3541: express-cookie-parser
- MAL-2025-4339: eslint-config-airbnb-compat
- MAL-2025-4029: ts-runtime-compat-check
- MAL-2025-2227: nyc-config
🎯 Advanced Malicious Package Analysis
🔍 Scan packages with malicious package detection enabled
# Real-time scanning
vet scan -D . --malware
# Timeout adjustment
vet scan -D . --malware \
--malware-analysis-timeout=300s
# Batch analysis
vet scan -D . --malware \
--json-dump-dir=./analysis
🎭 Specialized Scans
# VS Code extensions
vet scan --vsx --malware
# GitHub Actions
vet scan -D .github/workflows --malware
# Container Images
vet scan --image nats:2.10 --malware
# Scan a single package and fail if its malicious
vet scan --purl pkg:/npm/nyc-config@10.0.0 --fail-fast
# Active scanning of a single package (requires API key)
vet inspect malware \
--purl pkg:npm/nyc-config@10.0.0
🔒 Security Features
- ✅ Real-time analysis of packages against known malware databases
- ✅ Behavioral analysis using static and dynamic analysis
- ✅ Zero day protection through active code scanning
- ✅ Human in the loop for triaging and investigation of high impact findings
- ✅ Real time analysis with public analysis log
📊 Privacy and Telemetry
vet collects anonymous usage telemetry to improve the product. Your code and package information is never transmitted.
# Disable telemetry (optional)
export VET_DISABLE_TELEMETRY=true
🎊 Community & Support
🌟 Join the Community
💡 Get Help & Share Ideas
- 🚀 Interactive Tutorial - Learn vet hands-on
- 📚 Complete Documentation - Comprehensive guides
- 💬 Discord Community - Real-time support
- 🐛 Issue Tracker - Bug reports & feature requests
- 🤝 Contributing Guide - Join the development
⭐ Star History
🙏 Built With Open Source
vet stands on the shoulders of giants:
OSV • OpenSSF Scorecard • SLSA • OSV-SCALIBR • Syft
Created with ❤️ by SafeDep and the open source community
Star History
Repository Owner
Organization
Repository Details
Programming Languages
Tags
Topics
Join Our Newsletter
Stay updated with the latest AI tools, news, and offers by subscribing to our weekly newsletter.
Related MCPs
Discover similar Model Context Protocol servers
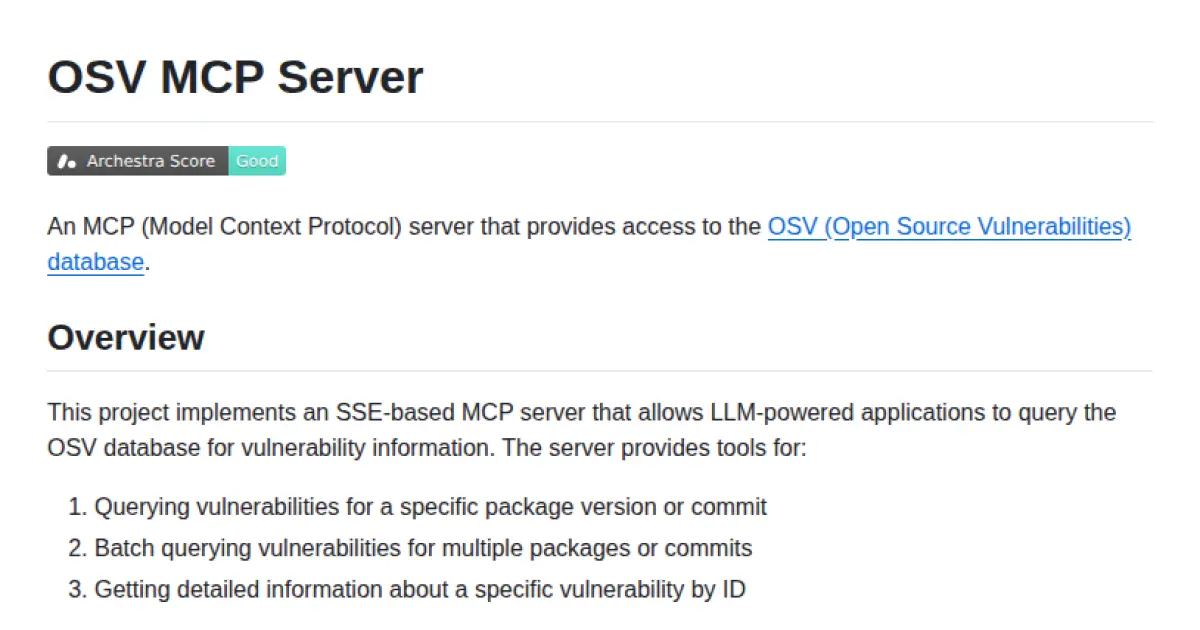
OSV MCP Server
SSE-based MCP server for querying the OSV vulnerability database
OSV MCP Server implements a Model Context Protocol (MCP) server that provides secure, programmatic access to the Open Source Vulnerabilities (OSV) database. It supports real-time streaming communication using SSE or streamable HTTP and allows querying of vulnerabilities for single or multiple packages, versions, or commits. The server is designed for integration with LLM-powered applications and supports configuration through environment variables and containerized deployments via ToolHive.
- ⭐ 25
- MCP
- StacklokLabs/osv-mcp
Semgrep MCP Server
A Model Context Protocol server powered by Semgrep for seamless code analysis integration.
Semgrep MCP Server implements the Model Context Protocol (MCP) to enable efficient and standardized communication for code analysis tasks. It facilitates integration with platforms like LM Studio, Cursor, and Visual Studio Code, providing both Docker and Python (PyPI) deployment options. The tool is now maintained in the main Semgrep repository with continued updates, enhancing compatibility and support across developer tools.
- ⭐ 611
- MCP
- semgrep/mcp
GitHub MCP Server
Connect AI tools directly to GitHub for repository, issue, and workflow management via natural language.
GitHub MCP Server enables AI tools such as agents, assistants, and chatbots to interact natively with the GitHub platform. It allows these tools to access repositories, analyze code, manage issues and pull requests, and automate workflows using the Model Context Protocol (MCP). The server supports integration with multiple hosts, including VS Code and other popular IDEs, and can operate both remotely and locally. Built for developers seeking to enhance AI-powered development workflows through seamless GitHub context access.
- ⭐ 24,418
- MCP
- github/github-mcp-server
Vibe Check MCP
Plug & play agent oversight tool to keep LLMs aligned, reflective, and safe.
Vibe Check MCP provides a mentor layer over large language model agents to prevent over-engineering and promote optimal, minimal pathways. Leveraging research-backed oversight, it integrates seamlessly as an MCP server with support for STDIO and streamable HTTP transport. The platform enhances agent reliability, improves task success rates, and significantly reduces harmful actions. Designed for easy plug-and-play with MCP-aware clients, it is trusted across multiple MCP platforms and registries.
- ⭐ 315
- MCP
- PV-Bhat/vibe-check-mcp-server
OPNsense MCP Server
AI-powered firewall and network management for OPNsense
OPNsense MCP Server provides a comprehensive Model Context Protocol server for automating and managing OPNsense firewall configurations. It enables AI assistants, such as Claude, to directly interact with and control networking features including firewall rules, NAT, VLANs, diagnostics, and advanced system operations via API and SSH. The tool supports batch operations, direct command execution, and advanced troubleshooting, enhancing network management automation. It also supports integration for infrastructure as code and toolchains supporting MCP environments.
- ⭐ 26
- MCP
- vespo92/OPNSenseMCP
Azure DevOps MCP Server
Standardized AI access to Azure DevOps via Model Context Protocol.
Implements the Model Context Protocol (MCP) to enable AI assistants to securely and efficiently interact with Azure DevOps resources. Provides a standardized bridge for managing projects, work items, repositories, pull requests, and pipelines through natural language interfaces. Supports modular authentication and a feature-based architecture for scalability and integration. Facilitates seamless integration with AI tools such as Claude Desktop and Cursor AI.
- ⭐ 306
- MCP
- Tiberriver256/mcp-server-azure-devops
Didn't find tool you were looking for?





